John is investing web-application firewall logs and observers that someone is attempting to inject the following :
char buff[10];
buff[10] = ‘a’;
What type of attack is this ?
Option 1 : Buffer overflow
Option 2 : CSRF
Option 3 : SQL injection
Option 4 : XSS
1. Buffer overflow
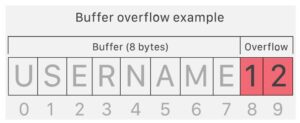
Buffer overflow this attack is an anomaly that happens when software writing data to a buffer overflows the buffer’s capacity, leading to adjacent memory locations being overwritten. In other words, an excessive amount of information is being passed into a container that doesn’t have enough space, which information finishes up replacing data in adjacent containers.
Buffer overflows are often exploited by attackers with a goal of modifying a computer’s memory so as to undermine or take hold of program execution.
What’s a buffer?
A buffer, or data buffer, is a neighborhood of physical memory storage wont to temporarily store data while it’s being moved from one place to a different . These buffers typically sleep in RAM memory. Computers frequently use buffers to assist improve performance; latest hard drives cash in of buffering to efficiently access data, and lots of online services also use buffers. for instance , buffers are frequently utilized in online video streaming to stop interruption. When a video is streamed, the video player downloads and stores perhaps 20% of the video at a time during a buffer then streams from that buffer. This way, minor drops in connection speed or quick service disruptions won’t affect the video stream performance.
Buffers are designed to contain specific amounts of knowledge . Unless the program utilizing the buffer has built-in instructions to discard data when an excessive amount of is shipped to the buffer, the program will overwrite data in memory adjacent to the buffer.
Buffer overflows are often exploited by attackers to corrupt software. Despite being well-understood, buffer overflow attacks are still a serious security problem that torment cyber-security teams. In 2014 a threat referred to as ‘heartbleed’ exposed many many users to attack due to a buffer overflow vulnerability in SSL software.
How do attackers exploit buffer overflows?
An attacker can deliberately feed a carefully crafted input into a program which will cause the program to undertake and store that input during a buffer that isn’t large enough, overwriting portions of memory connected to the buffer space. If the memory layout of the program is well-defined, the attacker can deliberately overwrite areas known to contain executable code. The attacker can then replace this code together with his own executable code, which may drastically change how the program is meant to figure .
For example if the overwritten part in memory contains a pointer (an object that points to a different place in memory) the attacker’s code could replace that code with another pointer that points to an exploit payload. this will transfer control of the entire program over to the
attacker’s code.
2. CSRF
Cross-site request forgery (also referred to as CSRF) may be a web security vulnerability that permits an attacker to induce users to perform actions that they are doing not shall perform. It allows an attacker to partially circumvent an equivalent origin policy, which is meant to stop different websites from interfering with one another .
What is the impact of a CSRF attack?
In a successful CSRF attack, the attacker causes the victim user to hold out an action unintentionally. for instance , this could be to vary the e-mail address on their account, to vary their password, or to form a funds transfer. counting on the character of the action, the attacker could be ready to gain full control over the user’s account. If the compromised user features a privileged role within the appliance , then the attacker could be ready to take full control of all the application’s data and functionality.
How does CSRF work?
For a CSRF attack to be possible, three key conditions must be in place:
• A relevant action. there’s an action within the appliance that the attacker features a reason to induce. This could be a privileged action (such as modifying permissions for other users) or any action on user-specific data (such as changing the user’s own password).
• Cookie-based session handling. Performing the action involves issuing one or more HTTP requests, and therefore the application relies solely on session cookies to spot the user who has made the requests. there’s no other mechanism in situ for tracking sessions or validating user requests.
• No unpredictable request parameters. The requests that perform the action don’t contain any parameters whose values the attacker cannot determine or guess. for instance , when causing a user to vary their password, the function isn’t vulnerable if an attacker must know the worth of the prevailing password.
3. SQL injection
SQL injection may be a web security vulnerability that permits an attacker to interfere with the queries that an application makes to its database. It generally allows an attacker to look at data that they’re not normally ready to retrieve. This might include data belonging to other users, or the other data that the appliance itself is in a position to access. In many cases, an attacker can modify or delete this data, causing persistent changes to the application’s content or behavior.
In some situations, an attacker can escalate an SQL injection attack to compromise the underlying server or other back-end infrastructure, or perform a denial-of-service attack.
What is the impact of a successful SQL injection attack?
A successful SQL injection attack may result in unauthorized access to sensitive data, like passwords, mastercard details, or personal user information. Many high-profile data breaches in recent years are the results of SQL injection attacks, resulting in reputational damage and regulatory fines. In some cases, an attacker can obtain a persistent backdoor into an organization’s systems, resulting in a long-term compromise which will go unnoticed for an extended period.
SQL injection examples
There are a good sort of SQL injection vulnerabilities, attacks, and techniques, which arise in several situations. Some common SQL injection examples include:
• Retrieving hidden data, where you’ll modify an SQL query to return additional results.
• Subverting application logic, where you’ll change a question to interfere with the application’s logic.
• UNION attacks, where you’ll retrieve data from different database tables.
• Examining the database, where you’ll extract information about the version and structure of the database.
• Blind SQL injection, where the results of a question you control aren’t returned within the application’s responses.
4. XSS
Cross-site scripting (also referred to as XSS) may be a web security vulnerability that permits an attacker to compromise the interactions that users have with a vulnerable application. It allows an attacker to bypass an equivalent origin policy, which is meant to segregate different websites from one another . Cross-site scripting vulnerabilities normally allow an attacker to masquerade as a victim user, to hold out any actions that the user is in a position to perform, and to access any of the user’s data. If the victim user has privileged access within the appliance , then the attacker could be ready to gain full control over all of the application’s functionality and data.
How does XSS work?
Cross-site scripting works by manipulating a vulnerable internet site in order that it returns malicious JavaScript to users. When the malicious code executes inside a victim’s browser, the attacker can fully compromise their interaction with the appliance .
What are the kinds of XSS attacks?
There are three main sorts of XSS attacks. These are:
• Reflected XSS, where the malicious script comes from the present HTTP request.
• Stored XSS, where the malicious script comes from the website’s database.
• DOM-based XSS, where the vulnerability exists in client-side code instead of server-side code.
Learn CEH & Think like hacker
- What is Ethical Hacking? & Types of Hacking
- 5 Phases of Hacking
- 8 Most Common Types of Hacker Motivations
- What are different types of attacks on a system
- Scope and Limitations of Ethical Hacking
- TEN Different Types Of Hackers
- What is the Foot-printing?
- Top 12 steps for Footprinting Penetration Testing
- Different types of tools with Email Footprinting
- What is “Anonymizer” & Types of Anonymizers
- Top DNS Interrogation Tools
- What is SNMP Enumeration?
- Top vulnerability scanning tools
- Information Security of Threat
- Footprinting tools:
- What is Enumeration?
- Network Security Controls
- What is Identity and Access Management?
- OWASP high TEN web application security risks
- Password Attacks
- Defend Against Key loggers
- Defend Against Spyware
- Covering Tracks
- Covering Track on Networks
- Everything You Need To Know About Sniffing – Part 1
- Everything You Need To Know About Sniffing – Part 2
- Learn more about GPS Spyware & Apparatuses
- Introduction of USB Spyware and It’s types
- 10 Types of Identity Theft You Should Know About
- Concepts of Denial-of-Service Attack & Distributed Denial of Service Attack
- Most Effective Ways to Overcome Impersonation on the Social Networking Site’s Problem
- How Dynamic Host Configuration Protocol (DHCP) Works
- DHCP Request/Reply Messages
- DHCP Starvation Attack
- Rogue DHCP Server Attack
- IOS Switch Commands
- Web Server Concept
- Web Server Attacks
- Web Server Attack Tools
- Web Server Security Tools
- 6 Quick Methodology For Web Server Attack
- Learn Skills From Web Server Foot Printing / Banner Grabbing
- The 10 Secrets You Will Never Know About Cyber Security And Its Important?
- Ways To Learn Finding Default Content Of Web Server Effectively
- How will Social Engineering be in the Future
- Understand The Background Of Top 9 Challenges IT Leaders Will Face In 2020 Now
- Learning Good Ways To Protect Yourself From Identity Theft
- Anti-phishing Tools Guide
This Blog Article is posted by
Infosavvy, 2nd Floor, Sai Niketan, Chandavalkar Road Opp. Gora Gandhi Hotel, Above Jumbo King, beside Speakwell Institute, Borivali West, Mumbai, Maharashtra 400092
Contact us – www.info-savvy.com



