Determine Data Security Controls
After assets have been identified and inventoried according to the level of classification, value, and sensitivity, identifying the types and rigor needed for security controls to protect the assets is the next step. There are numerous, proven security controls. With all security controls, the objective is to reduce risk to an acceptable level at a reasonable cost for the organization. Following a proven control design framework best assures a holistic approach to security. The framework also helps organize the process for resource allocation, investment of security spending, and measurement of security preparedness. Security controls help to identify, protect, detect, respond, and recover with respect to security risks to computer systems, data, or another information set. Some proven security control frameworks include the following:
- ISO/IEC 27001/27002 and ISO/IEC 27018: A family of standards that provide a systematic approach to formalizing risk management for an information security management system (ISMS) of people, processes, and technology controls. ISO/ IEC 27002 includes the catalog of suitable information security controls within the ISMS. ISO/IEC 27018 complements the other frameworks by providing standards for protecting PII in the cloud.
- NIST SP 800-53/53A: As mentioned before and as used with NIST 800-37, these are framework documents that inform many other related control standards sources. Although adequate and reasonable for use in commercial organizations, the NIST standards recommend security controls for U.S. federal information systems and organizations. They cover security controls for areas including incident response, access control, ability for disaster recovery, and business continuity. NIST SP 800-53A is used to document and assess security controls for effectiveness.
- Center for Strategic and International Studies (CSIS) Critical Controls for Effective Cyber Defense: Referred to as the 20 Critical Controls, this is a document outlining 20 crucial controls that form a risk-based minimum level of information security measures for an organization to implement. The controls are technical in design and focus on high-risk cyber attacks. They are a subset of the comprehensive controls found in other frameworks, most notably NIST SP 800-53/53A.
- Control Objectives for Information and Related Technologies (COBIT): Created by the international professional association ISACA, this recommends control objectives for a set of high-level requirements for effective control of each IT process. It subdivides IT into four domains (Plan and Organize, Acquire and Implement, Deliver and Support, and Monitor and Evaluate) and 34 processes.
- The Committee of Sponsoring Organizations of the Treadway Commission (COSO): With a view on information security as part of enterprise risk management, COSO originated from the financial industry and assists with integrating strategy and performance within overall enterprise risk management. The five components (Governance and Culture, Strategy and Objective-Setting, Performance, Review and Revision, and Information, Communication, and Reporting) in the updated framework are supported by a set of principles to assess effectiveness.
- FISMA: Established to produce several key security standards and guidelines required by congressional legislation. These publications include FIPS 199, FIPS 200, and NIST SPs 800-37, 800-39, 800-53, 800-53A, 800-59, 800-60, and 800-171.
Related Product : ISO 27001 Lead Auditor Training And Certification ISMS
Federal Risk and Authorization Management Program (FedRAMP): This is a U.S. federal government program that provides a standardized approach to security assessment, authorization, and continuous monitoring for cloud products and services.
- Department of Defense Instruction (DoDI) 8510.01: This is the Risk Management Framework (RMF) for DoD Information Technology and is meant to be scoped and tailored to DoD organizations with defense missions in the United States.
- The Australian Government Information Security Manual (ISM): Used for the risk-based application of information security controls mandatory for government agencies that conduct business under certain provisions outlined in the guide. The guide, however, is encouraged for all other government and commercial businesses. It provides best-practice guidance for making informed risk-based technical and business decisions and implementing strong information security measures. The purpose is to advise users on applying a risk-based approach to protecting their information and systems. The controls are therefore designed to mitigate the most likely threats to Australian government agencies.
- Information and Communication Technology (ICT) cybersecurity certification: The EU Commission has developed a common security certification framework for information and communication technology to increase trust and security in products and services that are crucial for the digital marketplace. The framework relies on integration of multiple international standards tailored to the EU organizations.
Technical, Administrative, and Physical Controls
Security control frameworks provide discipline and structure for the organization. They are typically made up of controls that are technical, administrative, and physical. A deeper understanding of each type of control is needed to emphasize the role each plays in securing organizational assets.
- Technical controls: The category of controls grouped as technical controls serve to use computer capabilities and automation to implement safeguards. The technical controls defend against misuse or unauthorized access to valuable information. In most organizations, a combination of technical controls is needed to work together to protect, detect, and respond to potential and actual security incidents and events. A few examples of technical controls related to asset management are the use of active and passive asset discovery tools to update the inventory, vulnerability scanning, and monitoring for unauthorized access to assets and data.
- Administrative controls: Also known as management controls, administrative controls are the policies, procedures, standards, and guidelines that an organization uses to implement technical and physical controls. The sources of administrative controls can be laws and regulations, industry best practices, and organizational mandates. Administrative controls inform the organization on roles and responsibilities, proper information protection practices, and enforcement actions if controls are not followed.
- Physical controls: As information and technology assets transform from paper based to digital and become more interconnected, physical controls, also referred to as operational controls, remain highly important. Controlling physical, human access to information assets is often the least expensive and most effective prevention control we can use. Designing asset protection programs that include guards and receptionists, entry access controls, area lighting and surveillance, closed circuit television (CCTV), and physical intrusion detection systems provides a layered defense approach.
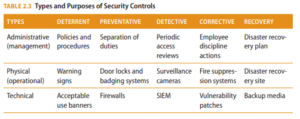
Note Physical, technical, and administrative controls are also defined by their protective purpose. Each type of control can be described as deterrent, preventative, detective, corrective, or recovery. Depending on the control, it may serve multiple functions in the overall security program.
Controls can be prioritized based on risks faced by the organization or specific threats. However, all of the controls work together to provide optimal security. For instance, administrative controls initiate policy and procedures that implement physical controls.
Technical controls may implement administrative requirements for access control. Physical controls may be needed to protect the organization’s data center, where computing equipment operates to implement technical controls. Security controls are also designated based on the scope of applicability for the control, the shared nature of the control, and the responsibility for control development, implementation, assessment, and authorization.
Administrative, technical, and physical controls are further designated as common controls, system-specific controls, and hybrid controls. Common controls are those that are inherited by multiple systems. System-specific controls are unique to one system. When one part of the control is common and another part of the control is system-specific, it is a hybrid control. A security professional is expected to understand how security controls work by type and designation, alone and in combination, to provide comprehensive asset security. Table 2.3 summarizes the types and designations of controls.
Follow Us
https://www.facebook.com/INF0SAVVY
https://www.linkedin.com/company/14639279/admin/


