Develop the Business Continuity Plan
The BCP itself is the organization’s commitment to maintaining the operations of the business. This plan focuses on the people, processes, and infrastructure on which the business relies to deliver goods and services to its customers. Based on the information derived from the BIA work, the organization can now begin to evaluate appropriate controls to align the MTDs with the RPO/RTOs. The full range of control categories is available to the planners. Controls that affect the likelihood of the event are generally preferable to those that affect the consequence, but the decisions will have to be made at the organizational level.
A number of high-level strategies can be incorporated into the plan to address various aspects of the people-processes-infrastructure challenge. By addressing the preferred approaches to control, the BCP will shape the subsequent planning efforts.
Preventive Strategies
One of the best ways to ensure business continuity is to prevent events from happening in the first place. Some of the more common preventive approaches include the following:
- Training: Organizational resilience relies on a competent workforce with sufficient depth to ensure that critical business functions can be recovered. Many organizations often have people in roles where that individual is the only one who can perform the function. These single points of failure can be addressed in many ways, including training others to perform the task and identifying outside resources with the skills, knowledge, and ability to perform the work. Regardless, the BIA process should identify these critical roles, and the BCP should address the organization’s preferred approach to addressing these risks.
- Hardening the infrastructure: Decreasing the likelihood that a compromise will occur may lead to developing a more disaster-resilient infrastructure. Implementing highly available environments such as system clusters, private clouds, mirrored systems working in conjunction with environmental redundancy such as backup power supplies, redundant electrical generation, and HVAC systems will decrease the likelihood of system failure. Beyond supporting the individual information systems, the environmental redundancies may also speed recovery of the business processes.
- Advanced backup technologies: For most enterprise organizations, the range of availability services in the current storage environments have broadly replaced legacy approaches to backing up large data stores. The ability to snapshot datasets, maintain multiple data mirrors, and use new approaches to engineering the storage environment for geographical distribution can enhance both the availability and the performance of the storage pools. Cloud-based storage can be provisioned relatively easily as objects and presented as block or volume storage, and in some cases, raw storage can be implemented as well. The cost of cloud-based storage can also be adjusted based on the performance tier needed by the organization. For some legacy environments, however, the legacy approach of full system backups supported by incremental and differential backups remains the practice of choice.
- Load balancing: Whether it is across systems in a single data center or whether the processing load is distributed to multiple data centers, load balancing increases system availability. Planning must take into account minimum expected loads, however, to ensure that the minimum service levels are available in the event of the partial failure of the environment.
- Threat monitoring: Threat monitoring provides the system operators with changes in the threat environment, potentially providing time to implement protections against the threat event. In many cases, this includes increased system logging and monitoring, but it may include reporting from outside threat monitoring services.
Related Product : Certified Information System Security Professional | CISSP
Strategies to Prepare for Handling Events
Once the event has occurred, a number of other strategies and controls may become relevant. Recovery in place is often the only alternative for an organization that is tied to serving a geographical area. In a large-scale disaster, it may be difficult to get employees back to the site, to transport equipment and supplies, and to provide for the physical security of the environment. Many times, a recovery-in-place will leverage a mobile site, brought to the location of the original (but now compromised) location.
Alternate sites are often used by organizations to meet their RTOs. Alternate sites are characterized as mirror, hot, warm, or cold, depending on the level of readiness to handle the processing activities from the primary site. Regulatory constraints often dictate that organizations maintain an alternate processing site.
Mirror sites are completely duplicated environments, with either site being able to support the entire processing load at any point in time. Supported through load balancing or hot swapping, this is one of the most expensive approaches but has the highest levels of availability.
Hot sites have all of the same processing capabilities as the primary site and data captured up to the RPOs. When activated, the hot site would be operational within the organization’s RTO. Hot sites can be internal (owned by the organization) or external (contracted through a vendor).
Cold sites are an empty shells that must be provisioned to meet the processing demand. Cold sites are often characterized as only having four walls, a roof, and a power plug. In the event of a disaster, the lead times for the build-out must be taken into account in the RTOs. Warm sites have some level of infrastructure and/or data available to support the recovery. The presence of any recovery capability less than a hot site or more than a cold site is a warm site.
Another alternate site approach is through some mutual assistance agreement. When two organizations have similar infrastructures, it may be possible for one organization to provide support to the other in a disaster. While attractive from a financial perspective, this approach is often challenging to implement, as most organizations run with little spare capacity and hosting another organization may have significant operational impacts on the host as well. This approach is most often found in governmental entities, implemented through a memorandum of agreement or similar vehicle.
Cloud bursting/hopping is one of the newest approaches to disaster recovery. For organizations with private cloud environments, it may be possible using provisioning tools such as Puppet/Chef, or vendor proprietary tools, to transition from an internal infrastructure to an external cloud infrastructure. For non–cloud-ready applications, or where large volumes of data must be moved to the cloud, additional planning must be undertaken to ensure the viability of the approach.
Documenting the Plan
The BCP identified in the chartering process sets an organizational tone for resilience. Focused on shaping the subsequent planning activities, the BCP should minimally address the following issues:
- Organizational resilience vision: The overall tone for the organization’s resilience activities should be characterized. It should reflect the compliance expectations, the commitments to customers, and a recognition of the general range of risk faced by the organization. If the organization is adopting an all-hazards approach to planning, this should be included in the vision to ensure that subsequent planning is properly aligned.
- Organizational resilience priorities: From the prioritization work performed in the BIA process, the organization should identify the critical business functions to focus the organization’s resources properly. The inclusion of a CBF as a priority should be explained in terms meaningful to the organization. Senior management’s identification of priorities should serve to minimize the ‘turf battles” inside the organization.
- Organizational risk framework: The processes and preferred strategies for addressing resilience should be identified. This should include the expectations for training and plan exercises.
- Roles and responsibilities: The organization should reaffirm the ownership of the BC process and explicitly identify who is responsible for maintaining the BCP, how the plan will be reviewed and on what schedule, and how BC information will be reported through the organization.
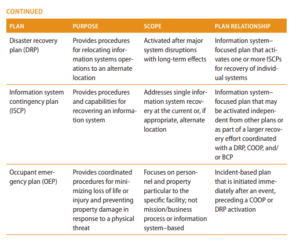
Once adopted, the BCP will allow the next level of planning to begin. Organizational requirements may dictate a number of separate plans; however, they should be integrated into, or aligned with, the overall BCP. As an example, NIST 800-34 identifies plans in the areas shown in Table 1.1. 
While different organizations may have unique requirements for planning, the subsequent plans themselves should address a number of areas.
- Invocation (or declaration): Clear standards should exist as to what circumstances invoke a particular plan and who in the organization is authorized to invoke a particular plan. Invoking an organizational response may incur both financial and reputational consequences, so it is essential that the appropriate level of management decide that the plan should be implemented. This includes identifying compliance requirements that the plan addresses, the potential event anticipation milestones, and the triggers that would cause changes in the organizational response.
- Recovery strategies: The plan should clarify the organization’s preferred recovery strategies for the incident. Unfortunately, not all incidents fall neatly into the plans that have been created. A well-designed plan will provide responders with some flexibility, including addressing workarounds and alternative recovery approaches. The recovery strategies should be refined to clarify the recovery priorities for the event.
- Organization: In an event, traditional lines of communication and authority maybe disrupted or modified. These changes need to be specified in the individual plans. The organization should identify the crisis event leadership, span of control and span of authority for each leadership level, in-band and out-of-band communications flows for notification and reporting, and the roles of the individual recovery teams and individuals.
- Communications: The range of stakeholders affected when any response plan is invoked may vary greatly. Internal and external customers and suppliers, vendors, regulators, various levels of management, and the individuals involved in the execution of the recovery will require different levels of detail from the organization. In a broad disaster, media and the general public might also have to be notified. All stakeholders must receive appropriate, timely information on which to act or make decisions. Failing to provide timely communications may also have financial or reputational consequences to the organization, separate from the actual impact of the event.
- Human resources: In many organizations, invocation of a plan may affect the use of people in the response. The scope and nature of the disaster, the effect the event has on the ability of people to do their work, labor or union contracts, and various statutory or regulatory requirements may affect who can respond to the event.
- Finance: The event may require the expenditure of funds in a very short time frame. Organizations that have complex contracting processes may often find themselves unable to acquire the goods and services necessary to effect a timely response. Indeed, in certain disasters, traditional mechanisms for acquiring goods through credit cards or purchase orders may simply be unavailable. Capturing the costs of the recovery itself for subsequent insurance or other recovery claims must also be handled in such a way as to facilitate the documentation of claims.
- End state: The plan should be clear on what level of capability must be recovered for the organization to declare the end of the response, and the milestones that mark the transition to normal business operations.
- Training and awareness: The plan should clarify the level to which the organization can demonstrate its response capability. The techniques for training the employees’ will vary depending on the level of capacity that the organization needs.
One of the challenges that planners face is to determine the level of detail the plan should contain. There is no easy answer, as this will be different for each organization. Best practice is that the plan should provide enough detail for an experienced individual, having never executed the plan, to meet the performance expectations for that role. This expectation takes into account the real possibility that the person who would be expected to fill the role or perform the task may be unavailable in the actual event.
Keep in mind that the broader topic of business continuity has many well-defined bodies of practice, often specific to a particular industry segment. The role of the CISSP is to advocate for good security practices in the business continuity process to guarantee the confidentiality, integrity, and availability of information throughout the BCM continuum.
Follow Us
https://www.facebook.com/INF0SAVVY
https://www.linkedin.com/company/14639279/admin/


