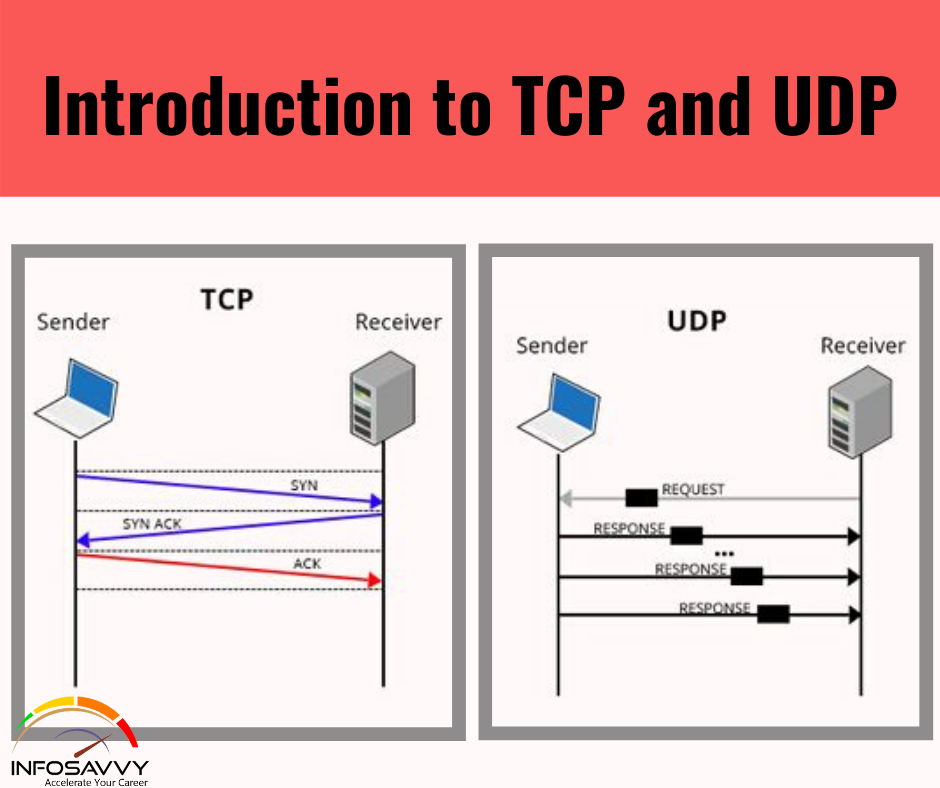
Introduction to TCP and UDP
Introduction to TCP and UDP in the OSI transport layer (Layer 4) defines several functions, the most important of which are error recovery and flow control. Likewise, the TCP/IP transport layer protocols also implement these same sorts of features. Note that both the OSI model and the TCP/IP model call this layer the transport layer. But as was common , when pertaining to the TCP/IP model, the layer name and number are supported OSI, so …