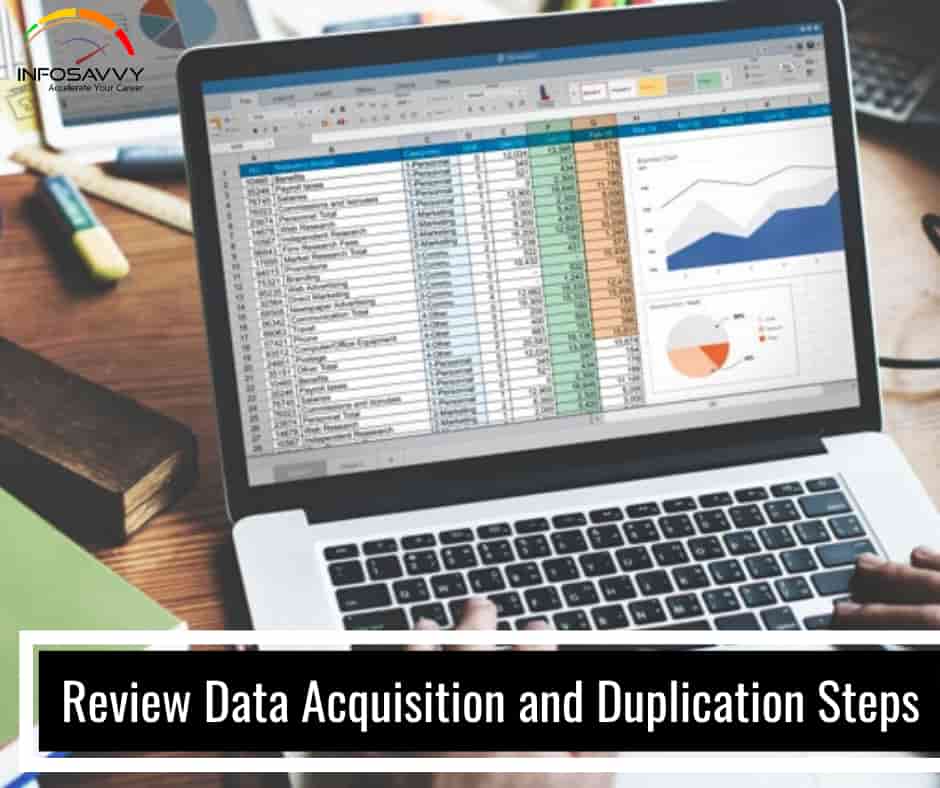
Data Acquisition and Duplication Tools: Software
Data Acquisition and Duplication Tools: Software in this article explain different types of software which is using in data acquision and duplication data tool. EnCase Forensic Source: https://www.guidancesoftware.com EnCase is a popular multi-purpose forensic platform which includes many useful tools to support several areas of the digital forensic process. This tool can collect a lot of data from many devices and extracts potential evidence. It also generates an evidence report. EnCase Forensic can help investigators …
Data Acquisition and Duplication Tools: Software Read More »