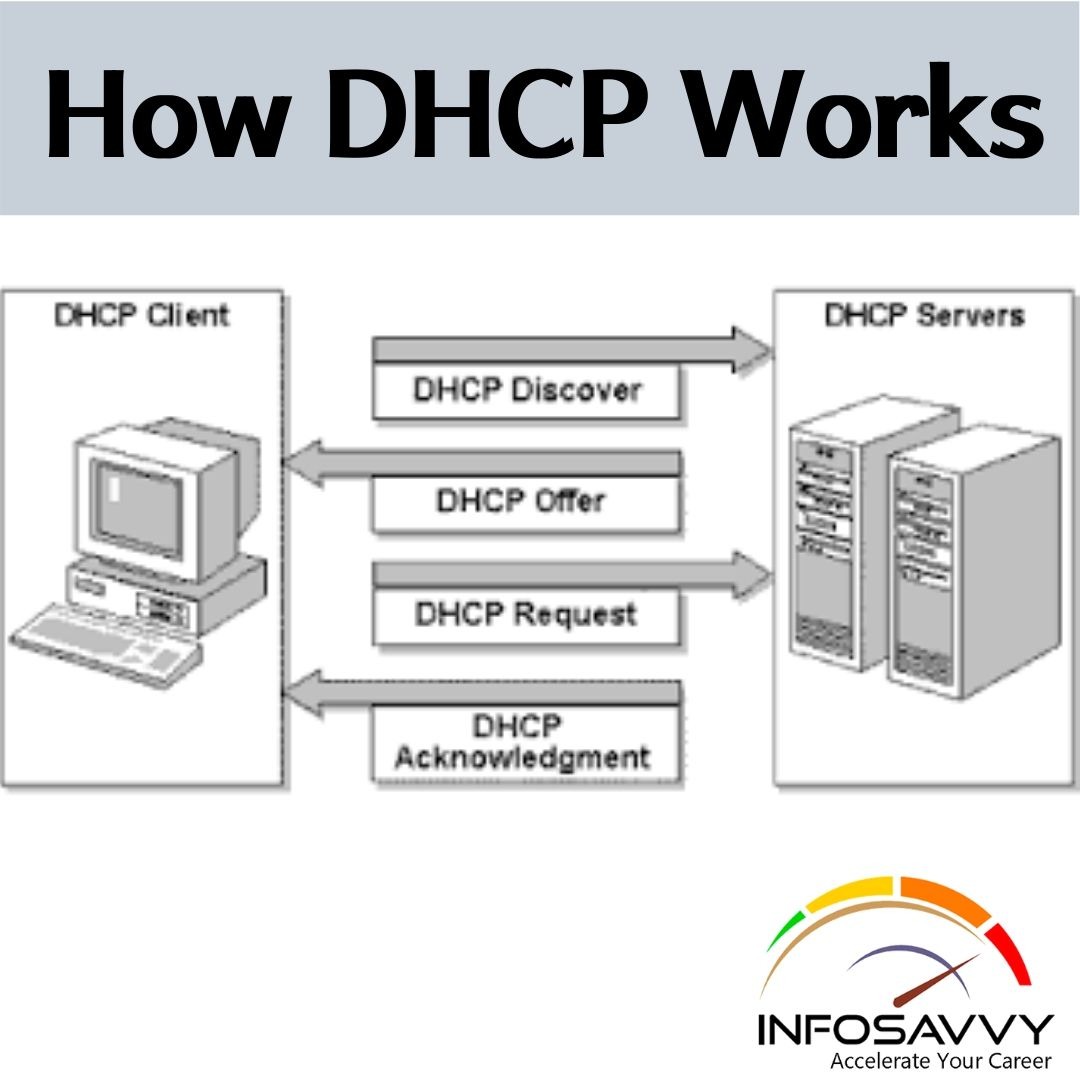
How Dynamic Host Configuration Protocol (DHCP) Works
Dynamic Host Configuration Protocol How Dynamic Host Configuration Protocol (DHCP) Works is a client/server protocol that gives an IP address to an IP host. additionally, to the IP address, the DHCP server also provides configuration-related information like the default gateway and subnet mask. When a Dynamic Host Configuration Protocol client device boots up, it participates in traffic broadcasting. DHCP can assign IP configuration to hosts connecting to a network. The distribution of IP configuration to …
How Dynamic Host Configuration Protocol (DHCP) Works Read More »