Everything You Need To Know About Sniffing – Part 2 in this Sniffing article you will learn about Protocols vulnerable, Hardware Protocol Analyzers, Wiretapping and its methods, Types of Wiretapping and Lawful Interception Protocols vulnerable to Sniffing.

Vulnerable to sniffing
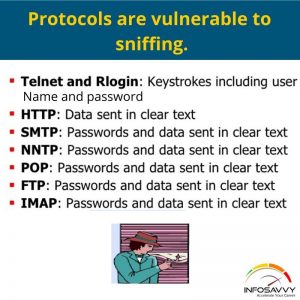
The following protocols are vulnerable to sniffing. The most reason for vulnerable to Sniffing these protocols is to accumulate passwords:
1. Telnet and Rlogin
Telnet may be a protocol used for communicating with a remote host (via port no. 23) on a network by using a instruction terminal. Rlogin enables an attacker to log into a network machine remotely via TCP connection. The protocols fail to supply encryption; therefore the data traversing between the clients connected through any of those protocols is in plain text and vulnerable to Sniffing, Attackers can sniff keystrokes including usernames and passwords.
Related Product : Certified Ethical Hacker | CEH Certification
2. HTTP
Due to vulnerabilities within the default version of HTTP, websites implementing HTTP transfer user data across the network in plain text, which the attackers can read to steal user credentials,
3. SNMP
SNMP may be a TCP/IP based protocol used for exchanging management information between devices connected on a network. The primary version of SNMP (SNMPv1) doesn’t offer strong security, which results in transfer of knowledge in clear text format. Attackers exploit the vulnerabilities during this version so as to accumulate passwords in plain text.
- Network News Transfer Protocol (NNTP) distributes, inquires, retrieves, and posts news articles employing a reliable stream-based transmission of news among the ARPA-Internet
- NNTP community, the protocol fails to encrypt the data which provides an attacker the chance to sniff sensitive information.
4. POP
The Post Office Protocol (POP) allows a user’s workstation to access mail from a mailbox server. A user can send mail from the workstation to the mailbox server via the simple Mail Transfer Protocol (SMTP). Attackers can easily sniff the data flowing across a POP network in clear text due to the protocol’s weak security implementations.
5. FTP
File Transfer Protocol (FTP) enables clients to share files between computers during a network. This protocol fails to supply encryption; so attackers sniff data also as user credentials by running tools like Cain & Abel.
6. IMAP
Internet Message Access Protocol (IMAP) allows a client to access and manipulate electronic message messages on a server. This protocol offers inadequate security, which allows attackers to get data and user credentials in clear text,
Sniffing within the data link Layer of the OSI Model
The Open Systems Interconnection (OSI) model describes network functions as a series of severs layers. Each layer provides services to the layer above it and receives services from the layer below.
The Data Link layer is that the second layer of the OSI model. During this layer, data packets are encoded and decoded into bits. Sniffers operate at the data Link layer and may capture the packets from the data Link layer. Networking layers within the 051 model are designed to work independently of every other; if a sniffer sniffs data within the data link layer, the upper OSI layer won’t be aware of the vulnerable to Sniffing.
Also Read : Everything You Need To Know About Sniffing – Part 1
Hardware Protocol Analyzers
A hardware protocol analyzer may be a device that interprets traffic passing over a network. It captures signals without altering the traffic segment. Its purpose is to monitor network usage and identify malicious network traffic generated by hacking software installed on the network. It captures a data packet, decodes it, and analyzes its content consistent with predetermined rules. It allows an attacker to see the individual data bytes of every packet passing through the network.
When compared to software protocol analyzers, hardware protocol analyzers are capable of capturing more data without packet drops at the time of data overload. Hardware protocol analyzers provide a good range of network connection options varying from LAN, WAN, and wireless to circuit-based Tel-co network lines. They’re capable of displaying bus states and low-level events such as high-speed negotiation (K/J chirps), transmission errors and re transmissions, etc. The analyzers provide accurate timestamps of the captured traffic. However, hardware analyzers are more expensive and have a tendency to be out of reach for individual developers, hobbyists, and ordinary hackers.
“We are changing the world With the Technology”
Hardware protocol analyzers from different companies include: N2X N5540A Agilent Protocol Analyzer Source:
The Agilent N2X is a test solution for testing the development and deployment of network services for converging network infrastructures. Service providers, network equipment manufacturers (NEMs), and component manufacturers can verify service attributes of the whole networks end-to-end, while also isolating problems right down to individual networking devices and subsystems. Two differing types of card are often configured simultaneously allowing test scenarios that use a mixture of port types.
Key sight E2960B
Key sight E2960B tests also as debugs. It includes a protocol analyzer that supports xl through x16 link widths, with intuitive spreadsheet style visualization. It offers EASY flow and context-sensitive display for a clear protocol viewing, the analyzer includes unique logic capabilities like lane view, fast ASPM sync time, and trigger an ordered set.
SPAN Port
Switched Port Analyzer (SPAN) may be a Cisco switch feature, also referred to as “port mirroring,” that monitors network traffic on one or more ports on the switch. SPAN port may be a port that’s configured to receive a replica of each packet that passes through a switch. It helps to analyze and debug data, identify errors, and investigate unauthorized network access on a network. When the port mirroring is on, the network switch sends a replica of the network packets from the source port to destination port, which studies the network packets with the assistance of a network analyzer. There are often one or more sources, but there should be just one destination port on the switch. Source ports are the ports whose network packets are monitored and mirrored. The user can simultaneously monitor the traffic of multiple ports, like the traffic on all the ports of a selected VLAN.
Wiretapping
Wiretapping or telephone tapping may be a method of monitoring telephone or Internet conversations by a third party with covert intentions. so as to perform wiretapping, the attacker first selects a target person or host on the network to wiretap then connects a listening device (hardware, software, or a mixture of both) to the circuit carrying information between two phones or hosts. Typically, the attacker uses little amount of electrical signal generated by the phone phone wires to tap the conversation, this enables attackers to watch , intercept, access, and record information contained within the data flow during a communication system.
Wiretapping Methods
The following are ways to perform wiretapping:
- The official tapping of telephone lines
- The unofficial tapping of telephone lines
- Recording the conversation
- Direct line wiretap
- Radio wiretap
Learn More about Investigation techniques in ECIHV2 from Infosavvy, Mumbai
“In Cyber Security the more systems we Secure,
The more Secure We all are.”
– Jeh Johnson
Types of Wiretapping
There are two sorts of wiretapping that an attacker can use to watch, record, and even alter the info flow within the communication system.
Active Wiretapping
In hacking terminology, active wiretapping is an MITM attack. This enables an attacker to watch and record the traffic or data flow during a communication system. The attacker also can after or injects data into the communication or traffic,
Passive Wiretapping
Passive wiretapping is snooping or eavesdropping. this enables an attacker to monitor and record traffic. By observing the recorded traffic flow, the attacker can snoop for a password or other information.
Note: Wiretapping without a warrant or the consent of the persons conducting the conversation may be a criminal offense in most countries, and it’s a punishable offense counting on the country’s law.
Lawful Interception
Lawful interception refers to legally intercepting data communication between two endpoints for surveillance on the normal telecommunications, VoIP, data, and multi service networks. Lawful interception (LI) obtains data from a communication network for analysis or evidence; this is often useful in activities like infrastructure management and protection, also as cyber security-related issues. Here, the network operator or service provider legally sanctions access to private network data for monitoring private communications like telephone calls and email messages. Such operations are carried out by the enforcement Agencies (LEAs).

This type of interception is important only to watch messages exchanged on suspicious channels during which the users are engaged in criminality. Countries round the world are making strides to standardize this sort of procedure for interception.
The figure above shows the Telco/ISP lawful solution provided by Decision Computer Group. the answer consists of 1 tap or access, and multiple systems for reconstruction of intercepted data. The tap/access switch collects traffic from the web service provider (ISP) network, sorts the traffic by IP domain, and serves it to the E-Detective (ED) systems that decode and reconstructs the intercepted traffic into its original format. The tool performs this with the assistance of supporting protocols like POP3, IMAP, SMTP, P2P and FTP, Telnet, etc. The Centralized Management Server (CMS) manages all the ED systems.
Questions related to this topic
- What are packets and protocols?
- What is hardware protocol?
- What are the 3 parts of a packet?
- What are the 4 parts of a packet?
Learn CEH & Think like hacker
- What is Ethical Hacking? & Types of Hacking
- 5 Phases of Hacking
- 8 Most Common Types of Hacker Motivations
- What are different types of attacks on a system
- Scope and Limitations of Ethical Hacking
- TEN Different Types Of Hackers
- What is the Foot-printing?
- Top 12 steps for Foot printing Penetration Testing
- Different types of tools with Email Foot printing
- What is “Anonymizer” & Types of Anonymizers
- Top DNS Interrogation Tools
- What is SNMP Enumeration?
- Top vulnerability scanning tools
- Information Security of Threat
- Foot printing tools:
- What is Enumeration?
- Network Security Controls
- What is Identity and Access Management?
- OWASP high TEN web application security risks
- Password Attacks
- Defend Against Key loggers
- Defend Against Spyware
- Covering Tracks
- Covering Track on Networks
- Everything You Need To Know About Sniffing – Part 1
- Everything You Need To Know About Sniffing – Part 2
- Learn more about GPS Spyware & Apparatuses
- Introduction of USB Spyware and It’s types
- 10 Types of Identity Theft You Should Know About
- Concepts of Denial-of-Service Attack & Distributed Denial of Service Attack
- Most Effective Ways to Overcome Impersonation on Social Networking Site’s Problem
- How Dynamic Host Configuration Protocol (DHCP) Works
- DHCP Request/Reply Messages
- DHCP Starvation Attack
- Rogue DHCP Server Attack
- IOS Switch Commands
- Web Server Concept
- Web Server Attacks
- Web Server Attack Tools
- Web Server Security Tools
- 6 Quick Methodology For Web Server Attack
- Learn Skills From Web Server Foot Printing / Banner Grapping
- The 10 Secrets You Will Never Know About Cyber Security And Its Important?
- Ways To Learn Finding Default Content Of Web Server Effectively
- How will Social Engineering be in the Future
- Understand The Background Of Top 9 Challenges IT Leaders Will Face In 2020 Now
- Learning Good Ways To Protect Yourself From Identity Theft
- Anti-phishing Tools Guide
This Blog Article is posted by
Infosavvy, 2nd Floor, Sai Niketan, Chandavalkar Road Opp. Gora Gandhi Hotel, Above Jumbo King, beside Speakwell Institute, Borivali West, Mumbai, Maharashtra 400092
Contact us – www.info-savvy.com



