Overview
Most organisations now rely on information systems to support all of their critical business processes. This dependency has led to an evolving risk from electronic security threats such as hacking, data loss, breach of confidentiality and even terrorism. These increasingly sophisticated attacks can come from individuals, private organisations or even clandestine foreign intelligence agencies. When these attacks result in loss of information, theft of confidential data or damage to critical systems and documents, organisation can suffer severe consequences including financial repercussions and reputational risk.
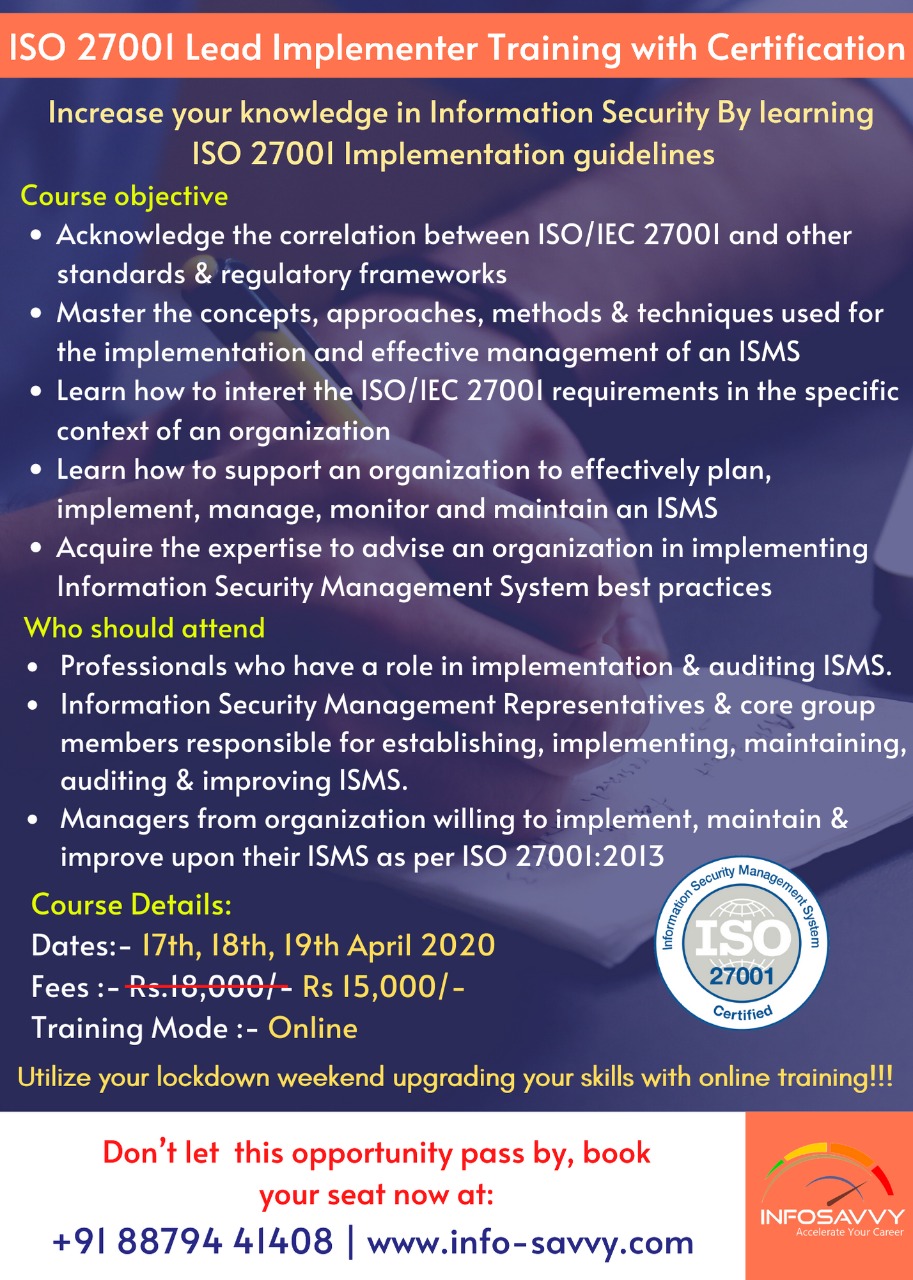
Certified Lead Implementer in ISMS
Apart from the course content of foundation level, following topics
shall also be covered in the Lead Implementer training
- ISO/IEC 27001 requirements along with implementation guidelines.
- Understanding the guidelines of ISO/IEC 27003 for Company’s ISMS policy
- Framing scope statement
- Setting information security objectives and action plan for objectives
- Documentation requirements
- Design of controls and writing procedures
- Risk management according to ISO/IEC 31000:2018Risk assessment, Risk analysis and risk treatment
- Incident management & Business continuity management
- Conducting internal audits and management review meeting.
- Continual improvement of ISMS through corrective action and analysis.
- Preparing for the ISO/IEC 27001:2013 audit
Check out what our students have to say
Overview
Most organisations now rely on information systems to support all of their critical business processes. This dependency has led to an evolving risk from electronic security threats such as hacking, data loss, breach of confidentiality and even terrorism. These increasingly sophisticated attacks can come from individuals, private organisations or even clandestine foreign intelligence agencies. When these attacks result in loss of information, theft of confidential data or damage to critical systems and documents, organisation can suffer severe consequences including financial repercussions and reputation at risk.
Course Outline For Certified Lead Implementer | ISO 27001
Certified Lead Implementer in ISMS
Apart from the course content of foundation level, following topics
shall also be covered in the Lead Implementer training
ISO/IEC 27001 requirements along with implementation guidelines.
Understanding the guidelines of ISO/IEC 27003 for
Company’s ISMS policy
Framing scope statement
Setting information security objectives and action plan for objectives
Documentation requirements
Design of controls and writing procedures
Risk management according to ISO/IEC 31000:2009 Risk assessment, Risk analysis and risk treatment
Incident management & Business continuity management
Conducting internal audits and management review meeting.
Continual improvement of ISMS through corrective action and analysis.
Preparing for the ISO/IEC 27001:2013 audit
Benefit
Your acquired knowledge and familiarity with ISO/IEC 27001 and ISO/IEC 27000 series during the training helps you and your organization in implementing an effective information security management system (ISMS).
An ISMS is based on the security awareness of the personnel, strong and stable processes and safe and secure IT systems and technologies.
You understand the phases of an audit and are able to assess the importance of actions to aid in continual improvement process in your IT organization.
Other IT Security and Governance Courses















Reviews
There are no reviews yet.